PKCS#7 (.p7b)
PEM (.crt)
PKCS#12 (.pfx)
After the certificate is issued, you can proceed with its installation on Tomcat server.
Depending on the certificate format in which you received the certificate from the Certificate Authority, there are different ways of importing the files into the keystore.
PKCS#7 (.p7b)
If the certificate you received is in PKCS#7 format (the extension of the certificate file will be .p7b or .cer), it already includes the necessary intermediate and root certificates. Additionally, a certificate with .p7b extension can be downloaded in the user account. Run the following command to import it into the keystore:
keytool -import -trustcacerts -alias tomcat -keystore example.jks -file example.p7b
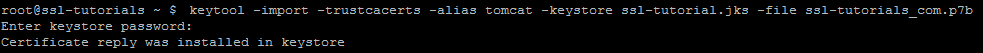
If the certificate was imported successfully, you will see the message ‘Certificate reply was installed in keystore’. You can check the details of the certificate that was imported to the keystore with a command:
keytool -list –keystore example.jks –v
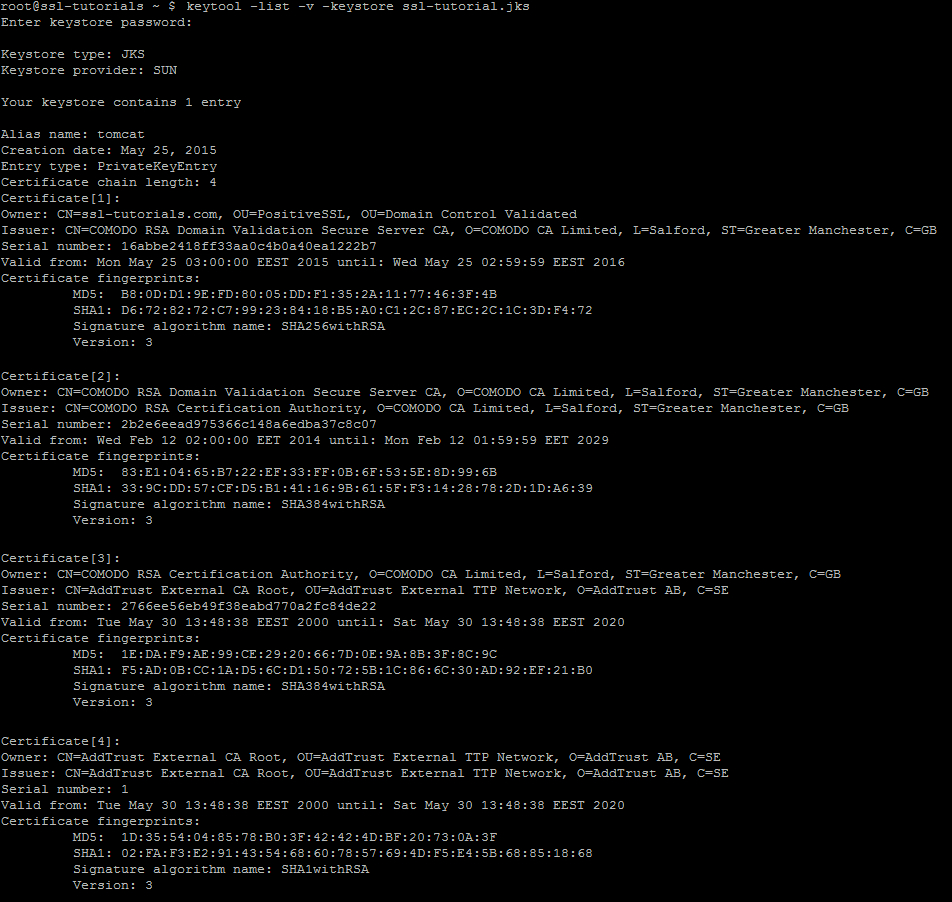
PEM (.crt)
If you received the certificate in the PEM format ( files will be with the .crt extension), you will need to import the root certificate, intermediate certificates and the certificate issued for your domain name to the keystore separately starting from a root certificate and ending with the certificate for your domain name.
To import a root certificate, run the following command:
keytool -import -alias root -keystore example.jks -trustcacerts -file root.crt
To import an intermediate certificate:
keytool -import -alias intermediate -keystore example.jks -trustcacerts -file intermediate.crt
!Note: Some certificates have several intermediate certificates, and all of them should be imported into the keystore in the correct order, starting from the certificate that was signed by the root and finishing with the intermediate certificate that signs the end-entity certificate for a domain. You need to use different aliases for different intermediate certificates. For example, for COMODO (now Sectigo) PositiveSSL certificate, first you need to import root certificate AddTrustExternalCARoot.crt, then intermediate certificate COMODORSAAddTrustCA.crt and finally, COMODORSADomainValidationSecureServerCA.crt
So, after the root and intermediate certificates are imported, import the certificate issued for the domain name with the following command:
keytool -import -alias tomcat -keystore example.jks -file example.crt
The alias should coincide with the one you indicated when creating the keystore.
After the successful import you need to edit Tomcat configuration file. As a rule, it is called server.xml and usually can be found in Home_Directory/conf folder.
By default it should look something like this:
<Connector port=”443″ protocol=”HTTP/1.1″
SSLEnabled=”true”
scheme=”https” secure=”true” clientAuth=”false”
sslProtocol=”TLS” keystoreFile=”/your_path/yourkeystore.jks”
keystorePass=”password_for_your_key_store” />
You need to modify the directive keystoreFile with the path to the location of your keystore file, and keystorePass with the password of the keystore.
If this is the first time you are configuring SSL certificate on Tomcat, first you will need to uncomment the SSL Connector configuration by removing the <!– and –> around the section you want to uncomment. Also, keystoreFile and keystorePass lines may be missing – you will need to manually enter these directives.
If your keystore contains more than one private key alias, you need to add ‘keyAlias’ directive with the reference to a needed alias.
keyAlias=”tomcat”
Save the changes and restart Tomcat web service.
PKCS#12 (.pfx)
If you have the key in PEM format, create the certificate in PKCS#12 format using this tool (PEM TO PKCS#12).
Other than that, use the following command:
openssl pkcs12 -export -out your_pfx_certificate.pfx -inkey your_private.key -in your_pem_certificate.crt -certfile CA-bundle.crt
To have .pfx or .p12 file working on Tomcat without unpacking it into a new keystore, you can simply specify it in the connector for the necessary port with keystoreType=”PKCS12“ directive added.
You can check the installation using this online tool.