Here we would like to explain the notifications related to HTTPS connection and SSL certificates in Chrome. After installing the certificate and browsing the site via https:// one may see the following warnings in Chrome:
- Your connection to this site is not fully secure. This page includes HTTP resources.
- Connection – obsolete connection settings.
- Your connection to this site is not secure. The certificate chain for this site contains a certificate signed with SHA-1.
- Your connection is not private. NET::ERR_CERTIFICATE_TRANSPARENCY_REQUIRED.
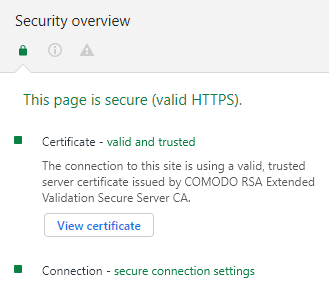
To check these messages in Chrome, click on the padlock icon.
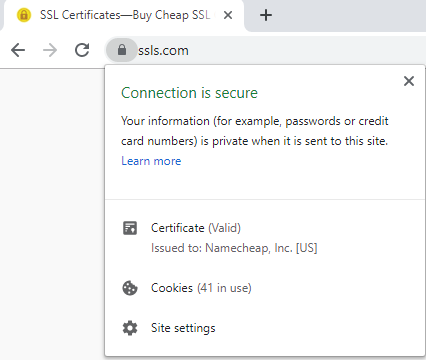
Note: From September 2023, a tune icon will replace the Chrome browser’s SSL padlock symbol. Google has explained that this is because a secure HTTPS connection is now the norm across the web. It should be noted that the tune icon should not be viewed as a trust indicator but as a way to give more detailed information about the connection and settings of a website.

Press Ctrl + Shift + J and check the Security tab.
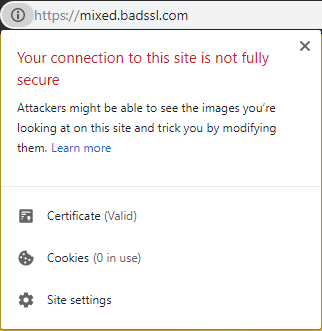
Your connection to this site is not fully secure. This page includes HTTP resources.
The window that pops up if you click on the padlock or tune icon contains the first part of the warning without any specific details:
You can find more details by checking the Security tab in the console after clicking Ctrl + Shift + J.
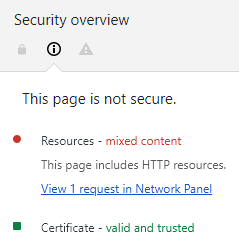
This warning is related to the insecure content issue and can be easily fixed by updating the links to all images, scripts, CSS or js files to use the secure HTTPS protocol. A good alternative is creating relative URLs in HTML code of web pages. More details on this matter can be found here.
Connection – obsolete connection settings
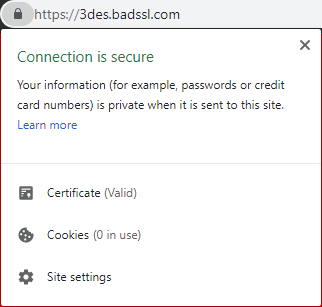
This error won’t be reflected in the security panel after clicking on the padlock or tune icon in the address bar:
However, if you press Ctrl + Shift + J >> Security, you’ll find the details about the cipher suites used during the connection.
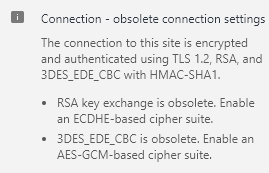
The cipher suite is used by a server to perform encryption and secure negotiation with clients. This issue is not related to the SSL certificate itself, as it is a specific server configuration that can be modified if you have root access. Otherwise, feel free to contact your server provider for assistance with this matter.
These articles on server SSL/TLS protocols and configuration may be useful:
Your connection to this site is not secure. The certificate chain for this site contains a certificate signed with SHA-1.
In the certificate details under the padlock/tune icon, you’ll see:
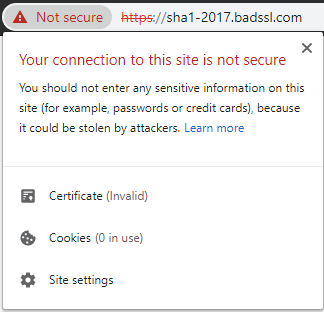
In the console (press Ctrl + Shift + J >> Security):
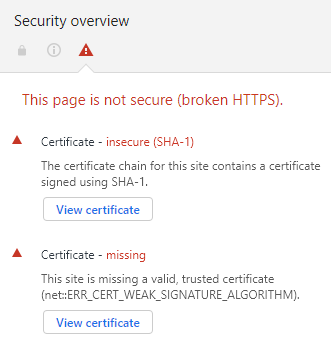
This warning usually appears for the web sites with the certificate installed long ago, as the Certificate Authorities used to sign certificates with SHA-1 signatures before. Now, this signature algorithm is deprecated due to its vulnerability to attacks. If you see this warning in Chrome, please reissue the certificate and reinstall it on the server.
We performed a full transition to SHA-2 in our system on November 6, 2014, so all the new and reissued certificates are signed with the latter-day sha256withRSAEncryption algorithm.
Note: This error is quite a rare case by 2019 as the SHA1 certificates are less and less used and are going to be completely terminated very soon. There are a few SHA1 root certificates left and most of the browsers already got acquainted to SHA2 root certificates. This error was mostly seen when the transition from SHA1 to SHA2 hashing algorithms was only beginning.
Your connection is not private. NET::ERR_CERTIFICATE_TRANSPARENCY_REQUIRED
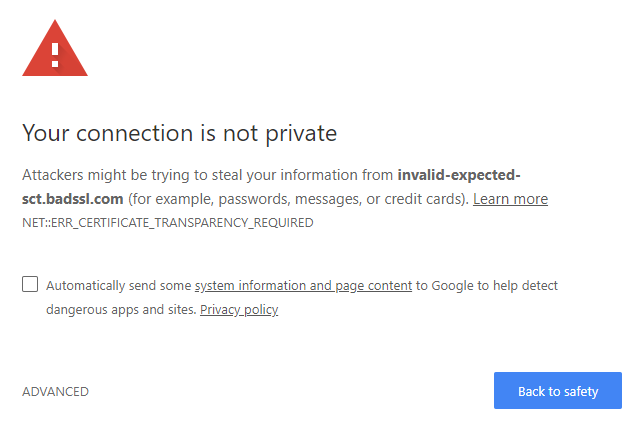
Currently, it is a requirement for all trusted Certification Authorities to submit all of the certificates they issue to at least 3 Certificate Transparency logs.
When the certificate records are missing in the Certificate Transparency logs for the site you are visiting, Chrome will display a security error when accessing the site.
If you’re not the site owner, there’s nothing you can do to fix the error, unfortunately. However, you can reach out to the site administrator and inform them about the issue providing the link to the page.
If you are the site owner, you should reissue your certificate or purchase a brand new one and install the new version on the server.
Since October 2017 all certificates we provide are added to the relevant Certificate Transparency logs automatically and immediately when the certificate is issued.
Note: Since 23 March 2018, all SSL certificates issued by Sectigo CA (former Comodo CA) comply with Chromium’s CT Policy.