One of the most important parts of SSL certificates’ security is the signature algorithm. The SHA-1 cryptographic algorithm, created nearly 20 years ago, is one of the most commonly used hash function for websites that are protected with SSL.
SHA-1 is getting weaker every day and is frequently exposed to collision attacks in which hackers may obtain fraudulent certificates. However, SHA-1 is still widely used for many websites that are protected with SSL.
Google and Microsoft encourage Certification Authorities and website administrators to upgrade their SSL certificates to use signature algorithms with hash functions that are stronger than 160-bit SHA-1 – such as SHA-2, which can produce up to 512-bit hash value and is supported almost everywhere.
According to a recent Google announcement, beginning November, users who visit websites that use SHA-1-based SSLs expiring any time in 2017 in updated Chrome 40 will see a warning that Google has recently announced that they’re sunsetting SHA-1. Initially, the warnings will be limited to a “Secure, but minor errors” icon, in the form of a lock with a yellow triangle. In later Chrome versions, this will become a red crossed-out lock.
According to web browser statistics collected from W3Schools’ log-files, Google Chrome is the most-used web browser. In September 2014, Google Chrome usage was at 60%, Mozilla Firefox 24%, and Microsoft Internet Explorer 10%.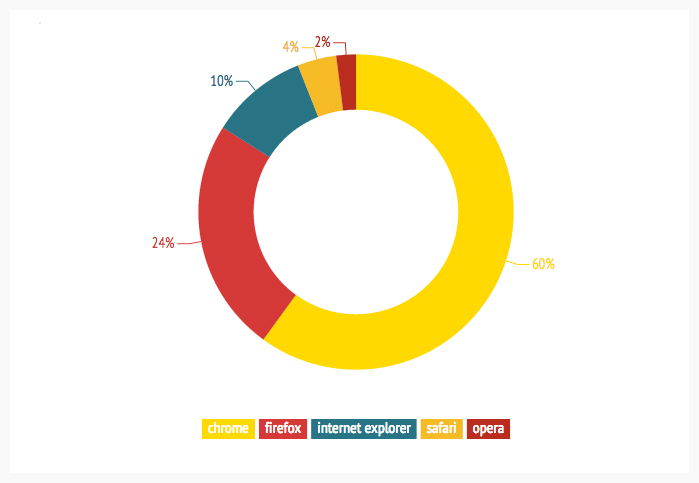 Here is a matrix showing important dates of changes in Chrome.
Here is a matrix showing important dates of changes in Chrome.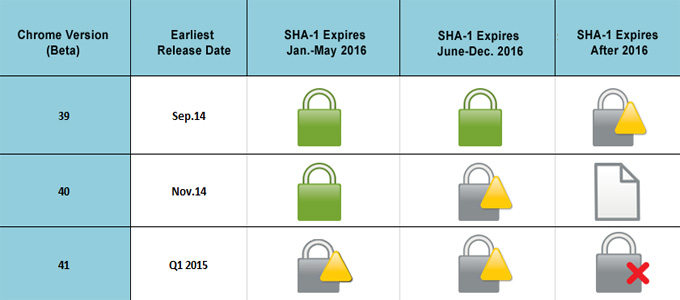
Mozilla’s CA Certificate Maintenance Policy also agrees that SHA-1 certificates should not be issued after January 1, 2016 or trusted after January 1, 2017.
What You Should Do:
- You may use this quick checker or this detailed SSL Server Test to check if your SSL certificate is using SHA-1 signature algorithm.
- Determine whether your server supports SHA-2. If your server supports SHA-2 and your SHA-1-signed SSL expires before January 1, 2016, reissue your certificate.
- If you need more information, please contact your CA or certificate shop. If you have a certificate with SSLs.com – you can reach out to us here.
SSLs web project promotion specialist
More than 10 years of experience in search engine optimization, contextual advertising, social media and web development.