No one was immune to the impact of cyber criminal activities in 2014. It will be remembered as the year of the Heartbleed bug that caused a vulnerability in the popular OpenSSL cryptographic library; the Poodle attack against outdated SSL 3.0; the sunset of the SHA-1 cryptographic algorithm, which was frequently affected by cyber attacks; and the Shellshock software bug.
Many e-commerce giants, popular smartphone applications, and government and health organizations were also actively attacked by hackers in 2014.
A vulnerability in the Snapchat app enabled criminals to steal 4.6 million usernames and phone numbers, as well as thousands of erased photos, using a third-party tool.
Moreover, hackers attacked the retail giant Ebay and stole 233 million users’ personal data, including usernames, passwords and contact details. Fortunately, no financial information was hacked, because it’s encrypted and stored separately.
Real-Time Cyber Attack Trackers
There are several cool online services that make it possible to track world cyber attacks in real time. The most usable are:
- Cyber threat map by FireEye, a sample of global cyber threat data collected from two-way sharing customers during the past 30 days. However, the “attacks today” counter does not represent real-time data. Rather, it provides real, observed attack rates and then calculates attacks for the day based on local time.
-
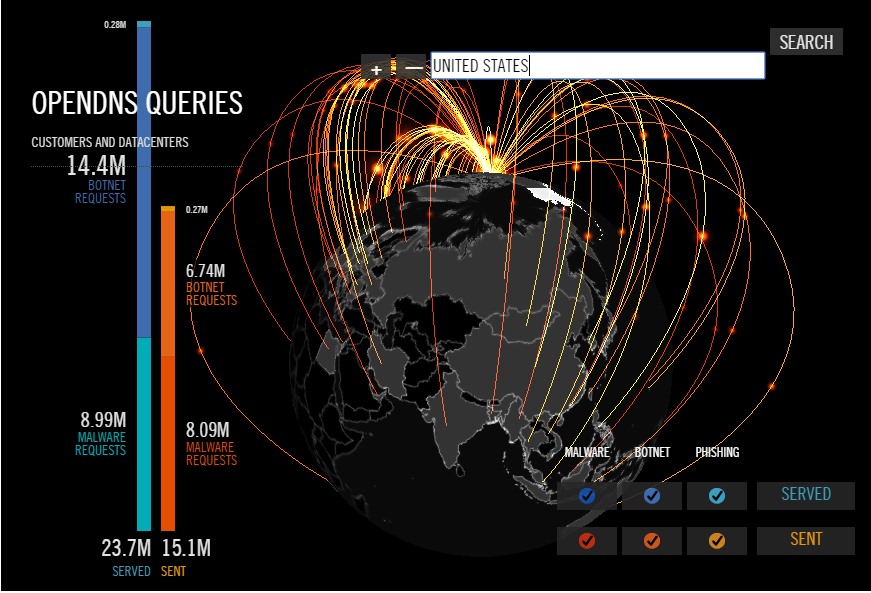
- OpenDNS GlobalNetwork, the world’s largest security network, created by OpenDNS, the leading provider of network security and DNS services. The platform handles more than 50 billion of the world’s internet requests daily, in 196 countries.
- IPViking by Norse Corp., a so-called hackers hunting map that represents real-time cyber attack data collected by IP Viking. It shows the exact coordinates and IP address of where an attack is going from, as well as which Norse system is under attack.
Top Security Threats Expected in 2015
Let’s take a look ahead at 2015 and define how it will be in terms of cybersecurity:
- The Insecurity of Things – The Internet of Things may be replaced with the Insecurity of Things in 2015. According to Robert Hansen, VP of WhiteHat Labs for WhiteHat Security, “In previous years the Internet of Things was not a big deal, but we’re seeing an increasing number of vulnerabilities in internet-capable devices, like TVs, home security systems, automation.”
- Advanced DDoS Attacks – According to the Annual Worldwide Infrastructure Security Report by Arbor Networks, the frequency of DDoS attacks nearly doubled in 2014, in comparison to 2013. Moreover, attacks continue to grow in volume, complexity, and frequency. For example, the largest DDoS attack reported in 2014 was 400 Gbps. Ten years ago, the largest reported attack was a mere 8Gbps.
- Targeting the “One Percent” – While cyber criminals may target a specific company or a government entity, they don’t generally spend time targeting an individual because the potential financial payoff isn’t worth their time. But wealthy consumers are the exception, said Coggeshall of LifeLock.
- Sophisticated Point-of-Sale Attacks – The goal of point-of-sale (PoS) attacks is to steal digital payment information. Any software that allows users or administrators to remotely access or control machines that are involved in financial operations, or that interacts in any way with PoS systems, is vulnerable to cyber-attack and needs to be extra protected against cyber criminals. McAfee Labs expects that PoS attacks will grow in 2015, though some retailers in the US have begun deploying chip-and-pin cards and card readers, which may help alleviate some of the threat.
- Ransomware Threat Transformation – Ransomware malware is a well-known type of scam that infects computers and restricts users’ access to some kinds of stored data. A user may not unlock it before paying a hacker hundreds or even thousands of dollars. The FBI has taken active steps to neutralize some of the more significant ransomware scams. Experts believe that in 2015 hackers will try to attack cloud networks such as Dropbox and Google Drive.
- The One-Time Password May Die – As we reported in a previous blog post, Bill Gates predicted the death of the password ten years ago. In 2014 hackers managed to steal the passwords of numerous iCloud celebrities’ accounts and to compromise the accounts of 76 million customers and seven million small businesses of JPMorgan Chase, one of the largest financial holding companies. These cyber-crimes show that passwords must be replaced with something more securable.
SSLs web project promotion specialist
More than 10 years of experience in search engine optimization, contextual advertising, social media and web development.