We’ve had questions from people scratching their heads about the difference between SSL Certificates and Code Signing Certificates. Because both use public-key encryption, are they interchangeable? The short answer is no. Let’s explore why.
Authentication & Encryption with SSL
Secure Sockets Layer (SSL) encryption protects users by authenticating servers (websites). There are different types of SSL Certificates, with three main types of authentication:
- Domain Validation SSL — authenticates the server, but the owner of the server and website business is unknown.
- Organization Validation SSL — authenticates the server and the business by checking it’s established in an official public listing like dnb.com or bloomberg.com.
- Extended Validation SSL — authenticates the server, and goes the extra mile in legitimising the business i.e. the Certificate Authority not only checks they’re in an official public listing, but also that they’re officially registered as a legal company with their local government, such as Inc. or LLC.
While authentication levels may differ, where all SSL Certificates are the same is their level of encryption. Protecting communication between websites and browsers with Hypertext Transfer Protocol Secure (HTTPS) is their main job. The way it works is when users enter a website, the SSL protection kicks in. And when typing in their email, delivery address, credit card details etc. on a website, the SSL encrypts the information as it travels from point A (browser) to point B (website server). Only the customer and the site Admin can unlock the details. Without this encryption, hackers could easily grab these private details in transit. That’s why websites without SSL Certificates are labelled as ‘Not secure’ by Google in the Chrome browser, and don’t display the closed padlock in browsers.
Authentication & Encryption with Code Signing
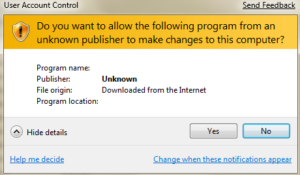
Code Signing Certificates use public key encryption for a totally different purpose. They protect users against shady software downloads by authenticating the identity of the software developer or publisher, and signing (validating) software to guarantee it hasn’t been tampered with (such as adding malicious code). When you try to download a piece of unsigned software, your browser or antivirus protection will kick in and warn you that the software originates from an unknown source. You’ll see a popup saying something like: ‘Do you want to allow this app from an unknown publisher to make changes to your device?’
With a Code Signing Certificate in place, your browser will know to trust the download without suspicion because it can verify the trustworthiness of the code. Sectigo also offers an Extended Validation version, which gives developers an added trust boost with Microsoft approval and a private key in the form of an external hardware token for added security. This has nothing to do with Extended Validation SSL Certificates though.
Other Differences
There are a couple more things that make SSL Certificates and Code Signing Certificates very different beasts:
- When an SSL expires, your website is no longer protected and will be flagged as ‘Not secure’ in search results. But if software has a valid Code Signing Certificate that has expired, no error warnings will be shown. That’s why it’s important to get your software from trusted sources.
- No chance using these two types of Certificates interchangeably. As we’ve explained, they have totally different purposes and will display error messages if you try.
Wrap Up
The difference between these two Certificates in a tidy nutshell is that one protects software, the other protects websites: Code Signing Certificates add a digital signature to software/code so it doesn’t get flagged with security warnings when people go to install it. They don’t actually encrypt software, just the signature and timestamp as part of what’s called an ‘authenticated signature block’. SSL Certificates protect websites and display as HTTPS urls. They encrypt ALL communication between user browsers and servers, keeping people protected when they engage with secured websites.

Cora is a digital copywriter for SSLs.com. Having eight years of experience in online content creation, she is a versatile writer with an interest in a wide variety of topics, ranging from technology to marketing.